[ad_1]
From time to time I pop my head up and have a look round to see the place RegRipper has been, and is being, used. My final weblog submit on this subject had fairly a couple of listings, however typically altering the search phrases reveals one thing new, or another person has determined to make use of RegRipper for the reason that final time I seemed.
References to RegRipper go means again, virtually so far as RegRipper itself (circa 2008):
SANS weblog (2009)
SANS weblog (2010)
SANS Infosec Handler’s Diary weblog (2012)
Kali Instruments (RR v2.5)
SANS Weblog, Mass Triage, pt 4 (2019)
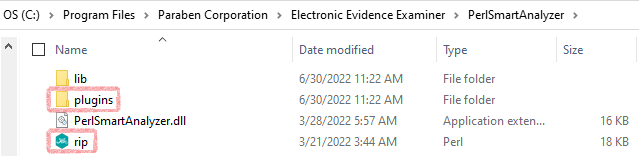
The newest industrial forensics platform that I’ve discovered that employs RegRipper is Paraben E3. I lately took a have a look at the analysis model, and located “rip.pl” (RegRipper v3.0 with modifications) within the C:Program FilesParaben CorporationElectronic Proof ExaminerPerlSmartAnalyzer folder, together with the “plugins” subfolder.
You possibly can see the Registry parsing in motion and the way it’s included into the platform on the Paraben YouTube Channel:
AppCompatCache parsing
Reviewing Knowledge from AmCache
Reviewing the movies, there’s one thing very acquainted in regards to the output illustrated on-screen. 😉
Different Sources (that incorporate RegRipper)
YouTube video by Ric Messier
CAINE forensics video
PacktPub Subscription
LIFARS Whitepaper on Shellbags
Home windows Registry Forensics, 1/e (PDF)
Paradigm Options weblog
Jason Shaver’s NPS thesis (2015)
That is only one extra step towards world domination! That is the place I tent my fingers and say “Wonderful” like Mr. Burns!
I discovered lately that James, the creator of the module, had up to date it in Sept, 2020. That is nice, however there are a couple of different tweaks I might made to the code, one which allowed me to test to see if hives are ‘soiled’.
[ad_2]
Source_link